[Sunil]: - Drop Uwsgi component entirely. After the changes, it mostly looks like Daemon component minus some features. One change that Uwsgi component does is when component is disabled, it also stops and disables the .service unit. Stopping the service is useful and we can add this to Daemon component. - Use /run instead of /var/run/ as 1) /var/run is a symlink to /run 2) /run/ path is what is listed in uwsgi-app@.socket unit file. - Implement upgrade for apps from older version. Disable and mask uwsgi init.d script. Enable the daemon component if the webserver component is enabled. - Update manifest files to deal with .socket units instead of 'uwsgi' service. Backup the /var/lib/private directories as that is actual directory to backup with DynamicUser=yes. - For bepasty load the configuration as a systemd provided credential since DynamicUser=yes. - Remove the /var/lib/private directories during uninstall. - Don't create user/group for bepasty as it is not needed with DynamicUser=yes. Tests: - Radicale - Functional tests pass - Freshly install radicale. - Web interface works. - Create and edit calendars - Path of the storage directory is in /var/lib/private/radicale (after accessing web interface) - Permissions on the storage folder and files inside are set to nobody:nobody. - Uninstall removes the /var/lib/private/radicale directory. - Create a calender and backup the app. Uninstall the app. Re-install the app. The calendar is not available. After restoring the backup, the calendar is available. - Install radicale without patch and create a calendar. Apply patches and start plinth.service. Setup is run. UWSGI is disabled and masked. Service is running. Old calender is visible. - Install radicale without patch. Disable and apply patches and start plinth.service. Setup is run. UWSGI is disabled and masked. Service is not running. Enabling the service works. - After upgrade, data storage path got migrated to /var/lib/private/radicale. Old data is accessible. - After upgrade the directory is still owned by radicale:radicale. - Freshly install radicale with patch and restore an old backup. The data is available in the web interface and data was migrated to /var/lib/private/radicale. - Bepasty - Functional tests pass - Freshly install bepasy. - Enabling and disabling rapidly works. - Uploading files works. - Path of the storage directory is /var/lib/private/bepasty. - Permissions on the storage folder are as expect 755 but on the parent are 700. - Permissions on the stored files are 644 and owned by nobody:nobody. - Uninstall removes the /var/lib/private/bepasty directory. - Upload a picture and backup the app. Uninstall the app. Re-install the app. The uploaded file is not available. After restoring the backup, the uploaded file is available. - Install bepasty without patch and upload a file. Apply patches and start plinth.service. Setup is run. UWSGI is disabled and masked. Service is running. Old uploaded picture is visible. - Install bepasty without patch. Disable app. Apply patches and start plinth.service. Setup is run. UWSGI is disabled and masked. Service is not running. Enabling the service works. - After upgrade, data storage path got migrated to /var/lib/private/bepasty. Old data is accessible. - After upgrade the directory is still owned by bepasty:bepasty. - Freshly install bepasty with patch and restore an old backup. The uploaded file is available in the web interface and data was migrated to /var/lib/private/bepasty. Signed-off-by: James Valleroy <jvalleroy@mailbox.org> Signed-off-by: Sunil Mohan Adapa <sunil@medhas.org> Reviewed-by: James Valleroy <jvalleroy@mailbox.org>
FreedomBox Service (Plinth)
The core functionality and web front-end of FreedomBox.
Description
FreedomBox is a community project to develop, design and promote personal servers running free software for private, personal communications. It is a networking appliance designed to allow interfacing with the rest of the Internet under conditions of protected privacy and data security. It hosts applications such as blog, wiki, website, social network, email, web proxy and a Tor relay, on a device that can replace your Wi-Fi router, so that your data stays with you.
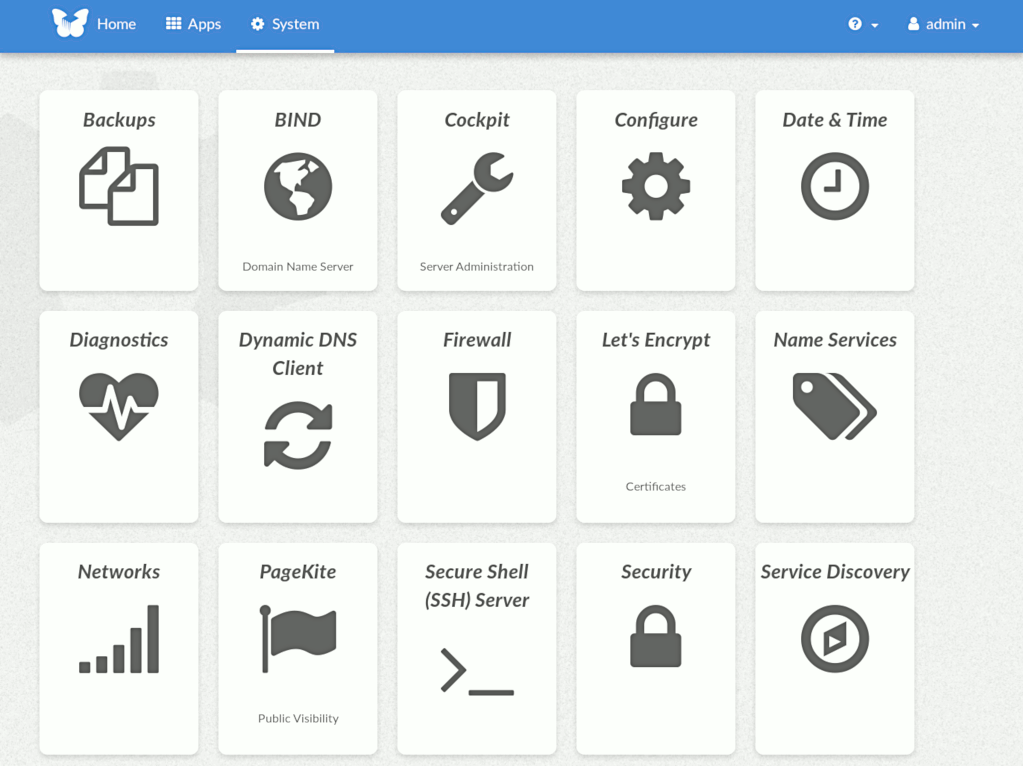
This module, called FreedomBox Service and also know as Plinth, is the core functionality and web interface to the functions of the FreedomBox. It is extensible and provides various applications of FreedomBox as modules. Each module or application provides simplified user interface to control the underlying functionality. As FreedomBox can act as a wireless router, it is possible to configure networking. It also allows configuration of basic system parameters such as time zone, hostname and automatic upgrades.
You can find more information about FreedomBox Service (Plinth) on the Plinth Wiki page, the FreedomBox Wiki and the FreedomBox Manual.
Getting Started
To have a running FreedomBox, first install Debian (Buster or higher) on a clean machine. Then run:
$ sudo apt install freedombox
Full instructions are available on FreedomBox Manual's QuickStart page.
For instructions on running the service on a local machine from source code, see INSTALL.md. For instructions on setting up for development purposes, see HACKING.md.
Contributing
See the HACKING.md file for contributing to FreedomBox Service (Plinth).
Localization
License
FreedomBox is distributed under the GNU Affero General Public License, Version 3 or later. A copy of AGPLv3 is available from the Free Software Foundation.