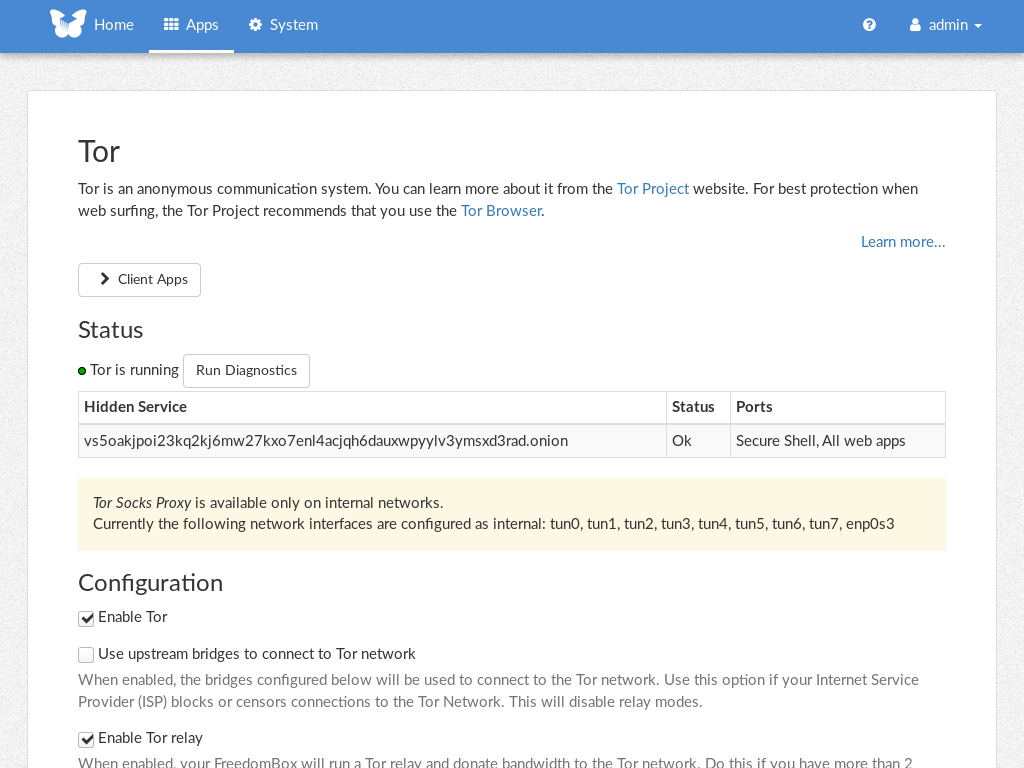
- Drop all the bash code. - Run the update URL code with same logic as before. Don't need to use action code for it. - Completely new way to handle configuration: using key/value store. Import old configuration once and delete it. - Use a glib scheduler instead of creating a cron job. - Store and show status from key/value store. - Handle multiple domains when getting/setting configuration and status. The UI still shows a single configuration form. To be improved later. - Catch and report all errors during the update process. - Drop all NAT detection code. - Drop selfhost.bz. German only, no free account, no proper TLS on domain, no easy to test. Existing accounts will continue to work with "other" as the service type. - For gnudip update code, add a timeout of 10 seconds, set a buffer size of two powers and fix handling error messages from server. Tests: - GnuDIP: - Upon submission of the form, the IP is updated if app is enabled. IP is not updated if app is disabled. - Every 5 minutes, check is made again and IP is updated. - If IP lookup URL is available, update calls are not made if the DNS is already up-to-date. - If IP lookup URL is not available, update calls are made unconditionally every 5 minutes. - For each of noip.com, freedns.afraid.org and other service: - Upon submission of the form, the IP is updated if app is enabled. IP is not updated if app is disabled. - Every 5 minutes, check is made again and IP is updated. - If IP lookup URL is available, update calls are not made if the DNS is already up-to-date. - If IP lookup URL is not available, update calls are made unconditionally every 5 minutes. - Form validation: - Domain field is always mandatory. - When type is selected as gnudip, the fields server, username, and password are mandatory. - When type is selected other than gnudip, the field update URL is mandatory. The rest are optional. - When the update URL contains a field contains <User>, username is mandatory. For <Pass>, password is mandatory. For <Ip>, ip_lookup_url is mandatory. - When use HTTP basic auth is checked, the fields username and password are mandatory. - Password is optional only if a previous password exists. If configuration is deleted from kvstore, password is mandatory. - Configuration import: Install dynamicdns without the patch. Add configuration with each of the service types. For GnuDIP service type, set two configurations with one with and without IP lookup URL. Update to code with the patch. Setup should run. - All fields in the configuration should be imported properly. - If the previous configuration is disabled, app should be disabled after import. Enabled otherwise. - Updating the IP address should work immediately after import. - Enable/Disable: when enabled, IP URL should be enabled every 5 minutes. When disabled, updates should not happen. - Status: - When status is removed from the DB, it should show that no status is available yet. - When the form is updated or update happens via the timer, the status is shown. It should show success for a proper update. Proper external IP address should be shown. - Set the server to localhost and submit. Status should show 'Server refused connection' message. IP address should be '-'. - Set the server to an unknown domain. Status should show 'Could not find server' message. IP address should be '-'. - Set the server to a known domain. Status should show 'Connection timed out' message. IP address should be '-'. - Last update time should keep increasing as time passes. - Backup/restore: - Functional tests. - Javascript: - When GnuDIP is selected as the type, the fields server, username, password, domain, show password, and IP lookup URL should be shown while other fields should be hidden. Same on page load with GnuDIP as pre-selected type. - When GnuDIP is not selected as the type, the fields update URL, accept all SSL certificates, use basic HTTP auth, domain name, username, password, show password, IP lookup URL and use IPv6 fields should be shown and rest of the fields should be hidden. Same on page load with non-GnuDIP as pre-selected type. - When show password is checked, password should be shown and when it is unchecked, password is masked. - When other service types are selected, the update URL values changes to the respective service's URL. Signed-off-by: Sunil Mohan Adapa <sunil@medhas.org> Reviewed-by: James Valleroy <jvalleroy@mailbox.org>
FreedomBox Service (Plinth)
The core functionality and web front-end of FreedomBox.
Description
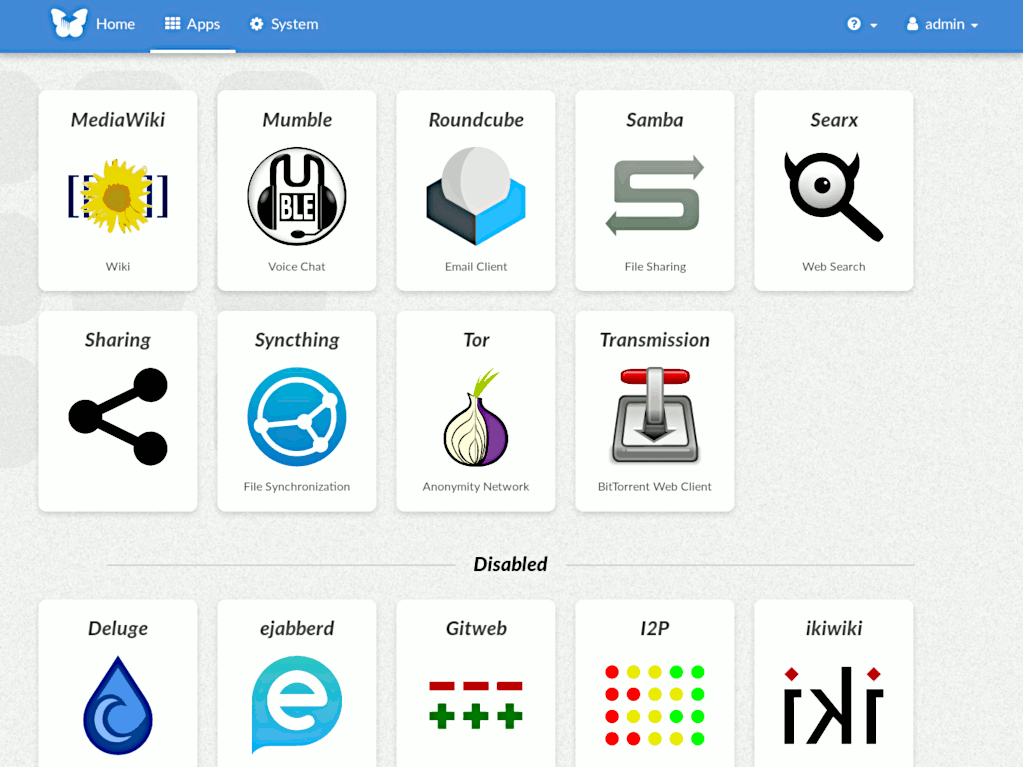
FreedomBox is a community project to develop, design and promote personal servers running free software for private, personal communications. It is a networking appliance designed to allow interfacing with the rest of the Internet under conditions of protected privacy and data security. It hosts applications such as blog, wiki, website, social network, email, web proxy and a Tor relay, on a device that can replace your Wi-Fi router, so that your data stays with you.
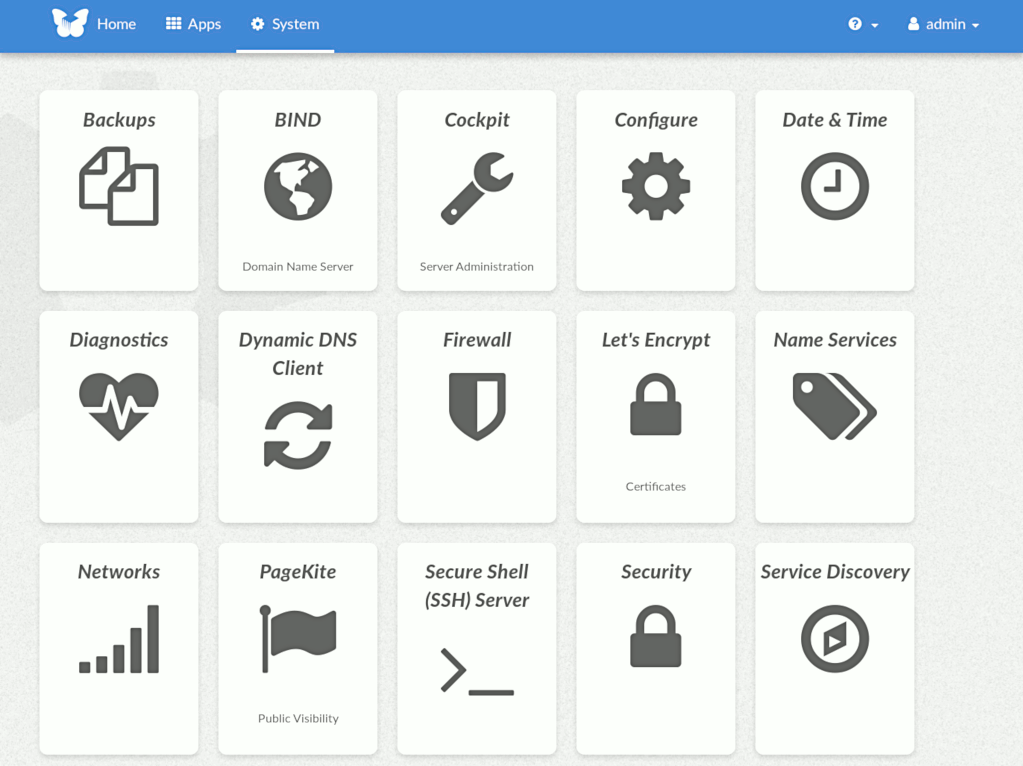
This module, called FreedomBox Service and also know as Plinth, is the core functionality and web interface to the functions of the FreedomBox. It is extensible and provides various applications of FreedomBox as modules. Each module or application provides simplified user interface to control the underlying functionality. As FreedomBox can act as a wireless router, it is possible to configure networking. It also allows configuration of basic system parameters such as time zone, hostname and automatic upgrades.
You can find more information about FreedomBox Service (Plinth) on the Plinth Wiki page, the FreedomBox Wiki and the FreedomBox Manual.
Getting Started
To have a running FreedomBox, first install Debian (Buster or higher) on a clean machine. Then run:
$ sudo apt install freedombox
Full instructions are available on FreedomBox Manual's QuickStart page.
For instructions on running the service on a local machine from source code, see INSTALL.md. For instructions on setting up for development purposes, see HACKING.md.
Contributing
See the HACKING.md file for contributing to FreedomBox Service (Plinth).